Die Zertifikate befinden sich The certificates are located in: | Translations Ignore |
|---|
| Code Block |
|---|
/etc/haproxy/haproxy.pem |
|
DieThe Korrektencorrect Berechtigungenpermissions sindare 400. (Nurread readonly fürfor root) and undcan könnenbe soset gesetztas werdenfollows: | Translations Ignore |
|---|
| Code Block |
|---|
chmod 400 haproxy.pem |
|
Die Datei enthält The file contains Sections: | Info |
|---|
| certificate chain: Private Key The end entity certificate and the matching private key are mandatory haproxy.pem - end_entity_cetificate.crt
- intermediate_certificate.crt
- root_certificate.crt
- private_key.key
Command to generate the haproxy.pem file
| Code Block |
|---|
| title | Generate the haproxy.pem file |
|---|
| $ cat end-entity.crt intermediate_certificate.crt root_certificate.crt private-key.key > haproxy.pem |
- Make sure the private key is not corrupted
$ openssl rsa -check -noout -in private_key.key
If the output “RSA key ok“ then the private key is correct. - Make sure the end entity certificate and the private key match together
Calculate the modulus of the of the private key $ openssl rsa -modulus -noout -in private_key.key | openssl md5
Calculate the modulus of the server certificate $ openssl x509 -modulus -noout -in end_entity_certificate.crt| openssl md5
If both outputs are identical then the private key matches to the end entity certificate. - The end entity certificate muss be in the first position and the matching private key muss be in the last position
- The intermediate(s) and the root certificate are optional. In case they are included, the intermediate(s) certificates muss before the root certificate
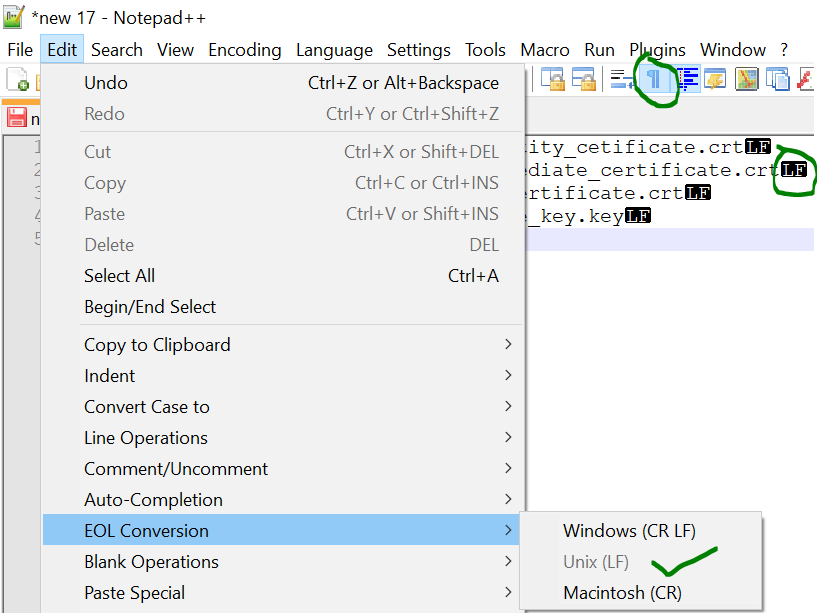
- Make sure the end of line (EOL) in the file are Linux EOL (LF). Windows EOL (CR LF) or Macintosh EOL (CR) will fail, because the Load Balancer is a Linux distribution.
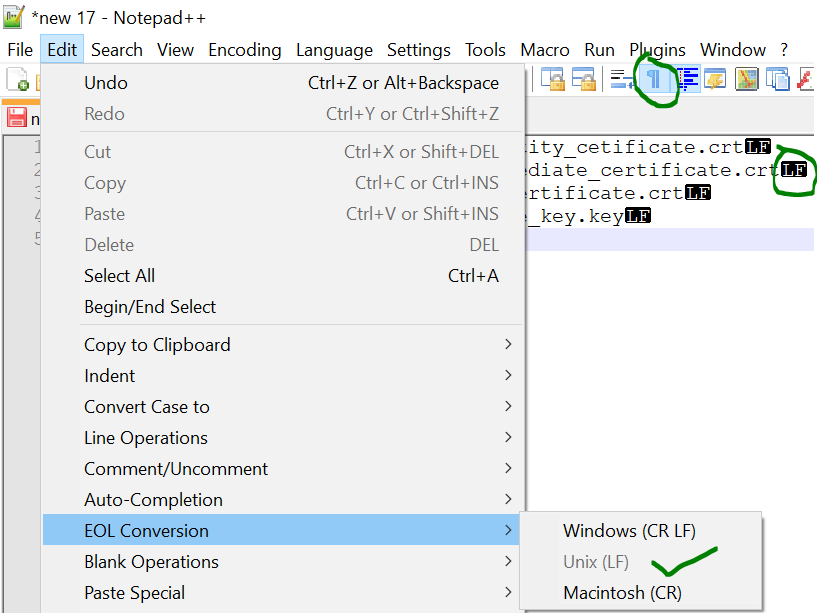 Image Added Image Added
- You can check the content (Check the Validity) after with this command:
$ openssl x509 -text -in haproxy.pem
|
| Translations Ignore |
|---|
| Code Block |
|---|
-----BEGIN CERTIFICATE----- |
MIIEzjCCA7agAwIBAgISESGiWLxseXetsJGbfZKEfehiMA0GCSqGSIb3DQEBCwUA |
MEwxCzAJBgNVBAYTAkJFMRkwFwYDVQQKExBHbG9iYWxTaWduIG52LXNhMSIwIAYD |
-----END CERTIFICATE----- |
-----BEGIN RSA PRIVATE KEY----- |
MIIEowIBAAKCAQEAsDGatsqSubHWmDG2IOVbocgwJfX9dB3EtXFw6HN87zDvAvvE |
9KUsDqMQiU2+aORZapzhl0oL1cfznPpQYyo4WGprQiNyL82TTxeWhCNRnBv4tnJw |
-----END RSA PRIVATE KEY----- |
|
Das Mindeste ist, dass der Zertifikat für den Load-Balancer sowie Private Key davon enthalten sind. Die Datei wird The minimum is that the certificate for the load balancer and private key are included. The file is referenced in haproxy.cfg referenziert: | Translations Ignore |
|---|
| Code Block |
|---|
frontend acdportal_https
mode http
bind :443 ssl crt /etc/haproxy/haproxy.pem #verify optional |
|
Falls ein Intermediate-Zertifikat eingefügt werden muss (Beispiel Sales-Force falls der Zertifizierungschain nicht bei SalesForce bekannt ist), kann dies wie folgt geschehen: - Rechter Mausklick auf die Zertifizierung im Browser:
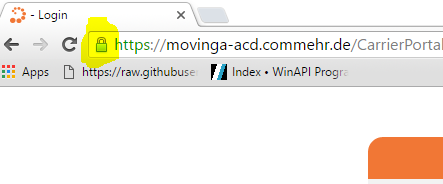 Image Removed Image Removed
- Details des Zertifikats anzeigen lassen:
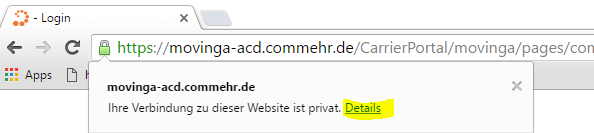 Image Removed Image Removed
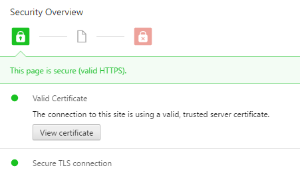 Image Removed Image Removed
- Intermediate Zertifikat anzeigen lassen:
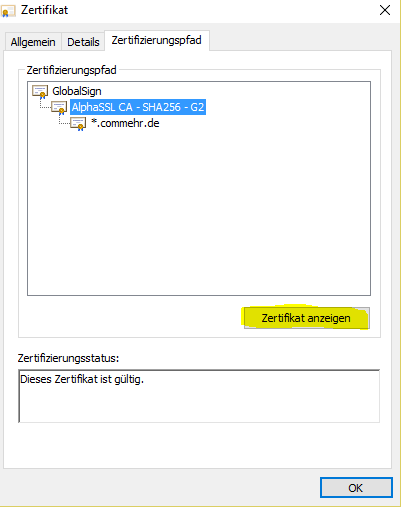 Image Removed Image Removed
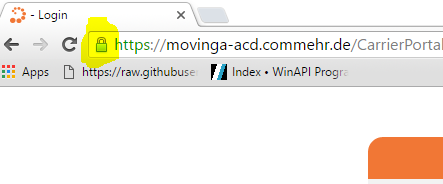
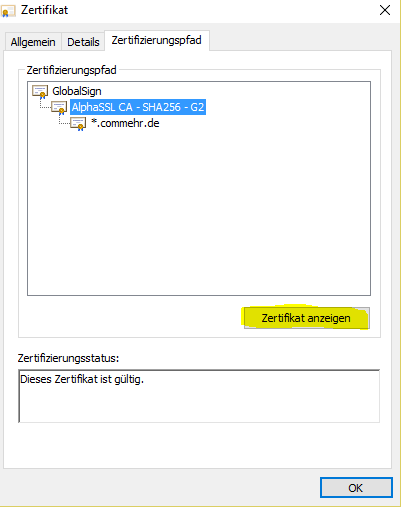
If an intermediate certificate must be inserted (example sales force if the certification chain is not known in SalesForce), this can be done as follows - Right mouse click on the certification in the browser:
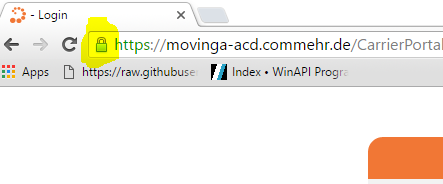 Image Added Image Added
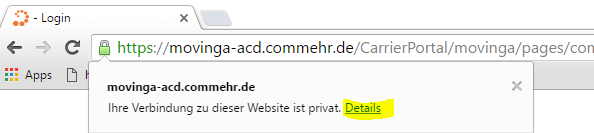
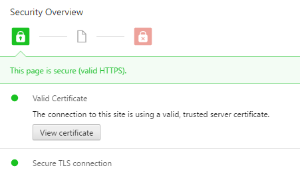
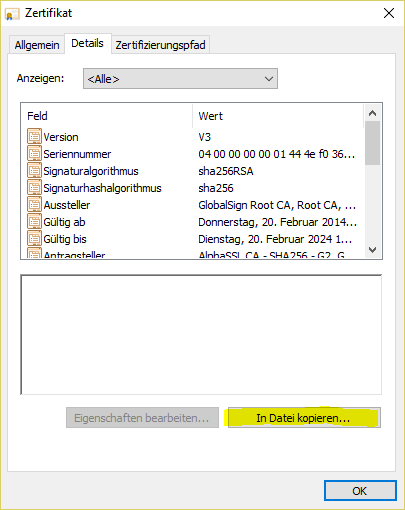
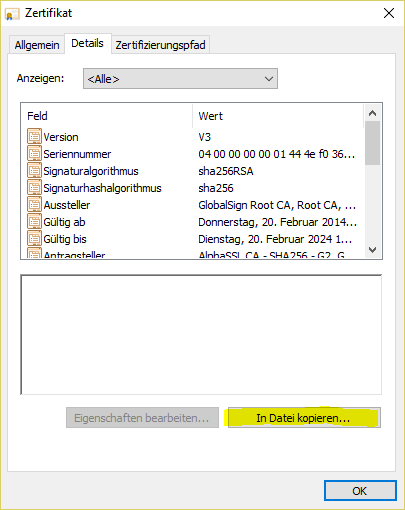
- Display details of the certificate:
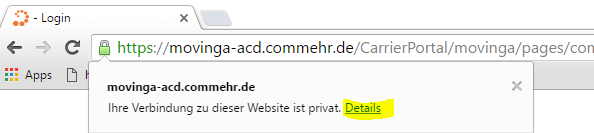 Image Added Image Added
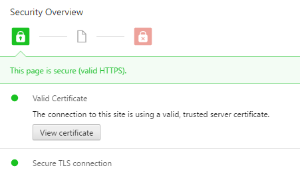 Image Added Image Added
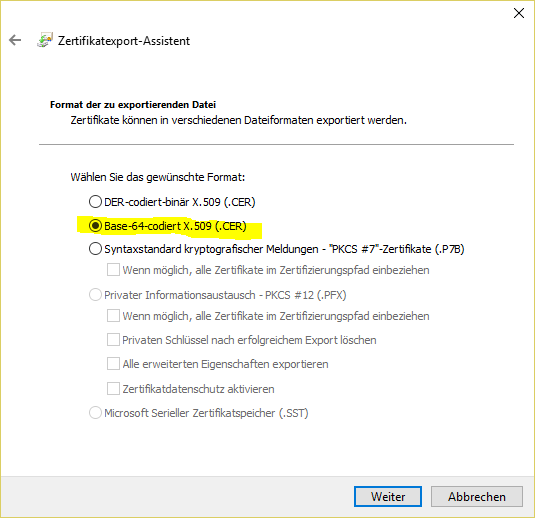
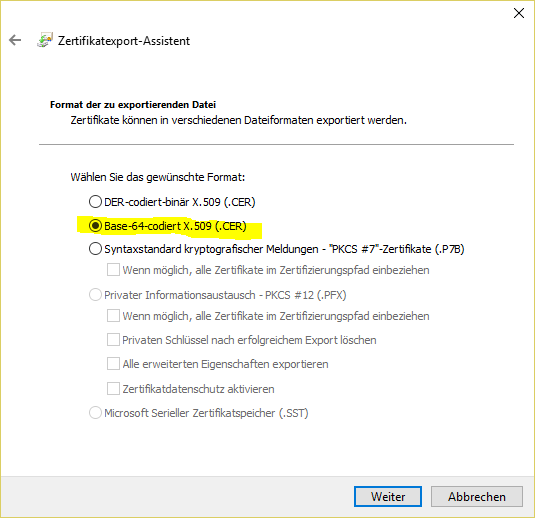
- Display intermediate certificate:
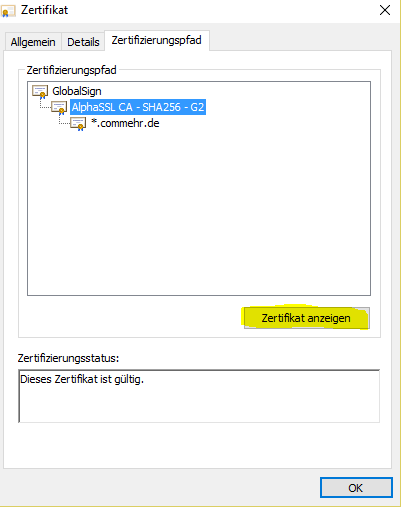 Image Added Image Added
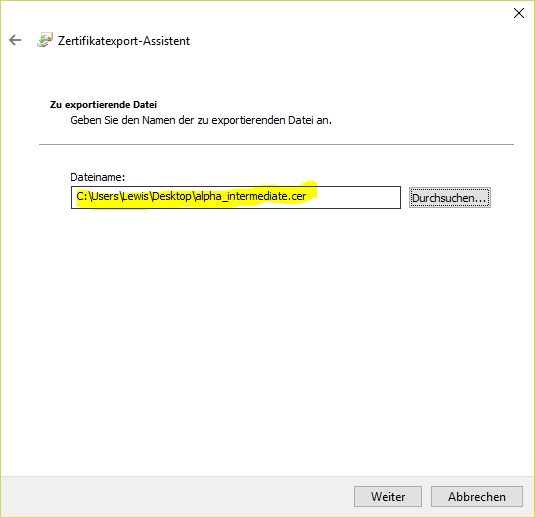
- Save as fileAls Datei speichern:
 # #
- Auf den lokalen Rechner speichernSave to the local computer:
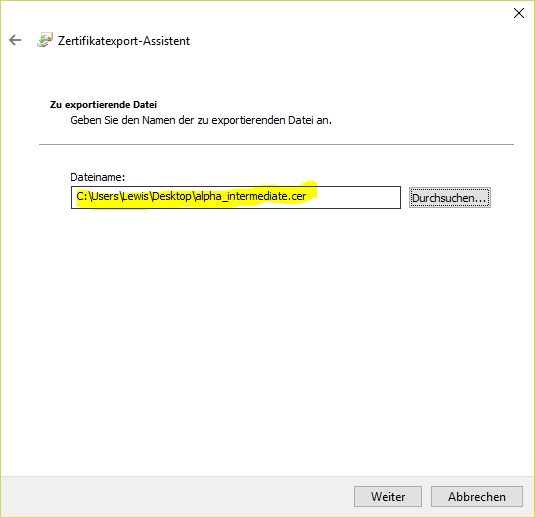
Die Datei dann mit einem Text-Editor editieren, dann den Inhalt des Intermediate-Zertifikats in die Datei haproxy.pem ganz unten hineinkopieren. Then edit the file with a text editor, then copy the content of the intermediate certificate into the haproxy.pem file at the very bottom. ThenDann: | Translations Ignore |
|---|
| Code Block |
|---|
service haproxy reload |
|
The following command can be used to convert a .pfx certificate file to .pem Format (the password for the certificate will be required): | Translations Ignore |
|---|
| Code Block |
|---|
openssl pkcs12 -in acd.cg.internal.pfx -out /root/haproxy.pem -nodes |
|
|