Introduction
To allow our applications to send e-mails as a given user or service account in Microsoft Entra, we need to configure an Azure AD application Microsoft Entra Active Directory application registration with the appropriate permission. Additionally, we need to ensure that the user or service account has a license assigned for sending e-mailspermissions.
Create an Azure AD App with Graph
...
permissions
...
You can do execute these steps using Azure PowerShell, the Azure CLI, or the Azure Portal that I'm doing for demonstration purposes.
Create a new App Registration Azure Portal
Head over to Azure AD and create a new App Registration.
- Azure Portal > Active Directory > App registrations > New registration
- Name: Whatever you want.
- Type: Accounts in this organizational directory only (Single tenant)
- Redirect URI: Not required.
Using a Client ID and Client Secret
Here's how you can set that up your applications to rely on the traditional Client ID / Client Secret approach for authenticating to the application.
We then need to create a new secret and securely store the value of the said secret, along with the Tenant ID and the app's Client ID.
From the App page:
- Certificates & Secrets > New client secret
- Copy the secret and store it in a safe location (password manager is a good idea).
...
. The steps required to enable Microsoft Graph SMTP authentication using the Azure Portal are described below.
Create App Registration
In the Azure Active Directory of your Tenant, navigate to App registrations and create a New registration. Choose a name and select "Register".
Create a User with permissions to use the Application
Navigate to Azure Active Directory → Users and create a new User
| Info |
|---|
If you already have a user which is used for the Microsoft Graph Teams Presence API App registration, you can use that user for this purpose again! |
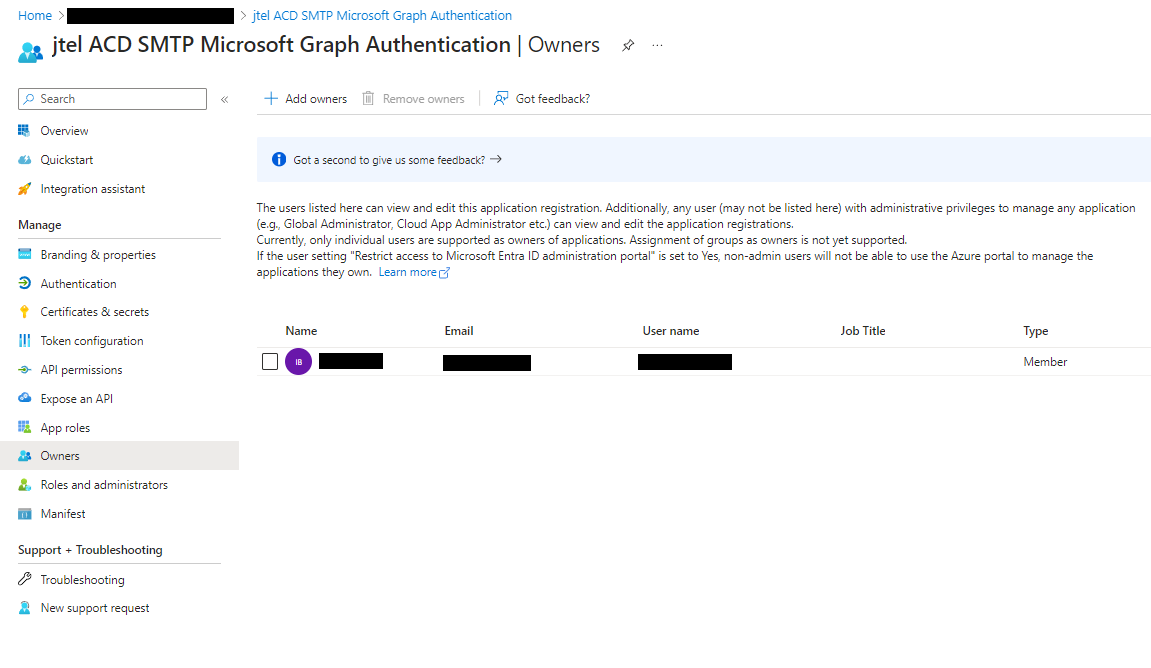
Assign the User to the Application
Navigate to the registered App configuration and into the tab "Owners" and add the User.
Grant Permissions
The Microsoft Graph SMTP Authentication requires permissions to send emails. Configure the following permissions with "Add a permission" and grant the permssions by clicking on "Grant admin consent for <Tenant Name>". The permission "User.Read" is added by default and should not be removed.
Create a Client Secret
Navigate to Certificates and Secrets and click on "New client secret" to add a new secret.
| Info | ||
|---|---|---|
| ||
As this secret will expire after the configured amount of time, please make note of this because it must be changed in the Client Master Data settings in your jtel ACD after being renewed in the Microsoft Entra Active Directory. |
Configuring Client Master Data
The newly Tenant ID, as well as the Application ID (Client ID) and
...
Client Secret (Secret Hash Value) are now configured in the jtel portal. The E-Mail Server and user also have to be changed, if you are switching to Office 365.
The configuration is added as Client Administrator in the Menu → Client Master Data in the email tab.
| E-Mail Sender | The E-Mail address which should be displayed as the sender |
| E-Mail Server | |
| Tenant ID | The Tenant ID of your Microsoft Entra AD |
| Client ID | The Client ID of the new registered Application |
| E-Mail User | The new user which is the owner of the registered Application |
| E-Mail Password | The Secret Hash Value |
At this point you should have stored these values for use later in our code:
- Application (client) ID.
- Directory (tenant) ID.
- The value of the secret you created for this app.
Set up the application permissions
Looking at the official docs for SendMail, we can see a few ways we can configure our apps to allow sending e-mails. Depending on your scenario, you may want to adjust the permissions between delegated or application permissions.
...
From the app page in the Azure Portal:
- API permissions > Add a permission
- Microsoft Graph > Application Permissions > Mail.Send > click Add Permission
Your configured permissions should look something like this:
...